For a system to perform well and ensure its
maintenance, it is extremely important to monitor and manage events on a
system. Event Logs are part of Windows system, that are created by on
a system and can be checked locally or remotely on regular intervals by an
administrator or any user. These logs can then be imported and viewed in a SIEM
tool to ensure the efficient Incident Response.
Table of Contents
·
Security Policy Settings
·
Advantage of security settings
·
Event Log
·
Account Management Events
·
Events in Windows 10 system
Security
Policy Settings
They are
set of rules that an administrator uses to configure a computer or multiple
devices for securing resources on a device or network. The Security Settings
extension of the Local Group Policy Editor allows you to define a security configuration
as part of a Group Policy Object (GPO).
The GPOs
are linked to Active Directory containers such as sites, domains, or
organizational units, and they enable you to manage security settings for
multiple devices from any device joined to the domain. Security settings
policies are used as part of your overall security implementation to help
secure domain controllers, servers, clients, and other resources in your
organization.
Advantage
of Security Setting
·
User are authenticated in a network or device.
·
The defined resources that any user is permitted to access.
·
Whether to record a user's or group's actions in the event
log.
·
Membership of a user in a group.
Event Log
The event logs usually keep a record
of services from various sources and then stores them in a single place. Events
logs can be of Security, System and Application event. As an incident
responder, you should look for multiple sources of log information and should
not forget to look at the older log files which may be present in backup
systems or volume shadow copies.
When the Event logs are assessed, the
Event ID have various field details with them;
Account Management Events
The Account
Management are extremely important and these events can be used to track the maintenance
of users, group, and computer objects in Local users and groups, Active
Directory.
Account
Management events can be used to track a new user account, any password resets,
or any new members being added to groups, or being deleted from the group.
The account
management events can be categorised into different types:
Events in Windows 10 system
To see how
this works, let’s get you started with Account Management Events.
To view the
security policy and setting, press ‘Windows+R’ and type
secpol.msc
Here you see that in audit policies,
there is ‘no auditing ‘ being displayed and to view these event we need to
activate them.
When you open the properties of audit
account management, check the success and failure attempts and press ok.
You can see that the security setting
has been updated and now the logs for account management are active.
Now to Open Event Viewer, press ‘Windows+r’
and type
eventvwr.msc
So, let’s check the logs created by
these events. Power on your Windows 10 systems.
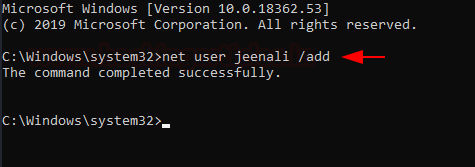
Event ID 4720
To see how this works, open
command-prompt, create a new user.
Net user username /add
After you create a new user, you can
see below that 4720 event is created and you can also see the account name.
Event ID 4722
After a new user account is enable,
you can see the event 4722 is generated with the account name.
Event ID 4724
When the password for a user account
was changed, it displays that an attempt to change the password was successful.
Event ID 4725
To disable a user account using
command prompt, you can type
Net user username /active:no
When you successfully disabled an
account the results in the event viewer are displayed as below.
Event ID 4726
To delete a user account using
command prompt, you can type
net user username /delete
When the account is deleted
successfully, this event is created and the user account name is also
displayed.
Event ID 4731
Go to local users and groups and
created a new group. Here you see that a new group is created named ignite.
When a new security enabled local
group is created, you can see that this event will be generated in the Event
viewer with its name.
Event ID 4732
To add a new member to the
security-enabled local group, type
Net localgroup groupname usernme /add
You see that the new member is added
to the group and the user name is also displayed.
Event ID 4733
As a member is removed from the
group, this event is generated.
Event ID 4734
To delete a security enabled group
using command-prompt, you can type,
Net localgroup groupname /delete
When the security enabled local group
is deleted, this event is generated and the name of the deleted group is also
displayed.
Event ID 4735
When the security enabled local group
is changed, this event is generated and the name of the group is also
displayed.
Event ID 4738
When the user account is changed,
this event is displayed.
Event ID 4798
When
a local user’s group is enumerated, you see that this log is created.
Conclusion: These
were the Account management events in Windows 10, to view more on Windows
Server 2016, you can click here.














































0 comments:
Post a Comment