Kali linux is often thought of in many instances, it’s one
of the most popular tools available to security professionals. It contains all
the robust package of programs that can be used for conducting a host of
security based operations. One of the many parts in its division of tools is
the forensics tab, this tab holds a collection of tools that are made with the
explicit purpose of performing digital forensics.
Forensics is becoming increasingly important in today’s
digital age where many crimes are committed using digital technology, having an
understanding of forensics can greatly increase the chance of making certain
that criminals don’t get away with a crime.
This article is aimed at giving you an overview of the forensics
capabilities possessed by Kali Linux.
So, let’s start with the programs as they appear in the
forensics menu:
Autopsy
A tool used by the military, law enforcement and entities
when it comes time to perform forensic operations. This package is probably one
of the most robust ones available through open source, it combines the
functionalities of many other smaller packages that are more focused in their
approach in one neat application with a web browser based UI.
It is used to investigate disk images. When you click on
Autopsy, it starts the service and its user interphase can be accessed on the
web browser at https://9999:Localhost/autopsy. It gives the user a full
range of options required to create a new case file: Case Name, Description,
Investigators Name, Host name, Host time zone, etc.
Its functionalities include – Timeline analysis, keyword
search, web artifacts, hash filtering, data carving, multimedia and indicators
of compromise. It accepts disk images in RAW or E01 formats and generates
reports in HTML, XLS and body file depending on what is required for a
particular case.
Its robustness is what makes it such a great tool, be it
case management, analysis or reporting, this tool has you covered.
Binwalk
This tool is used while dealing with binary images, it has
the capability of finding embedded file and executable code by exploring the
image file. It is a very powerful tool for those who know what they are doing,
if used right, it can be used to find sensitive information hidden in firmware
images that can be used to uncover a hack or used to find a loophole to
exploit.
This tool is written in python and uses the libmagic
library, making it perfect for usage with magic signatures created for Unix
file utility. To make things easier for investigators, it contains a magic
signature file which holds the most commonly found signatures in firmware’s,
making it easier to spot anomalies.
Bulk Extractor
This is a very interesting tool, when an investigator is
looking to extract certain kind of data from the digital evidence file, this
tool can carve out email addresses, URL’s, payment card numbers, etc. This is
tool works on directories, files and disk images. The data can be partially
corrupted or it can be compressed, this tool will find its way into it.
The tool comes with features which help create a pattern in
the data that is found repeatedly, such as URL’s, email ids and more and
presents them in a histogram format. It has a feature by which it creates a
word list from the data found, this can assist in cracking the passwords of
encrypted files.
Chkrootkit
This program is mostly used in a live boot setting. It is
used to locally check the host for any installed rootkits. It comes in handy
trying to harden an endpoint or making sure that a hacker has not compromised a
system.
It has the capability to detect system binaries for rootkit
modification, lastlog deletions, quick and dirty string replacements and utemp
deletions. This is just a taste of what it can do, the package seems simple at
first glance but to a forensic investigator, its capabilities are invaluable.
Foremost
Deleted files which might help solve a data incident? No
problem, Foremost is an easy to use open source package that can carve data out
of formatted disks. The filename itself might not be recovered but the data it
holds can be carved out.
Foremost was written by US Air Force special agents.
It can files by referencing a list of headers and footers even if the directory
information is lost, this makes for fast and reliable recovery.
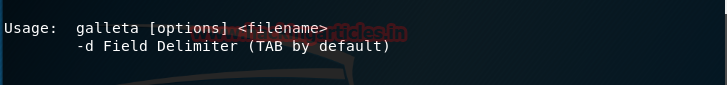
Galleta
When following a trail of cookies, this tool will parse them
into a format that can be exported into a spreadsheet program.
Understanding cookies can be a tough nut to crack, especially
if the cookies might be evidence in a cybercrime that was committed, this
program can lend a hand by giving the capability to structure the data in a
better form and letting you run it through an analysis software, most of which
usually require the data to be in some form of a spreadsheet.
Hashdeep
This program is a must when dealing with hashes. Its
defaults are focused on MD5 and SHA-256. It can be existing files that have
moved in a set or new files placed in a set, missing files or matched files,
Hashdeep can work with all these conditions and give reports that can be
scrutinized, it is very helpful for performing audits.
One of its biggest strengths is performing
recursive hash computations with multiple algorithms, which is integral when time
is of the essence.
Volafox
This is a memory analysis tool that has been written in
Python, it is focused towards memory forensics for MAC OS X. It works on the
Intel x86 and IA-32e framework. If you’re trying to find malware or any other
malicious program that was or is residing on the system memory, this is the way
to go.
Volatility
Probably one of the most popular frameworks when it comes to
memory forensics. This is a python based tool that lets investigators extract
digital data from volatile memory (RAM) samples. It is compatible to be used
with majority of the 64 and 32 bit variants of windows, selective flavors of
Linux distros including android. It accepts memory dumps in various forms, be
it raw format, crash dumps, hibernation files or VM snapshots, it can give a
keen insight into the runtime state of the machine, this can be done
independently of the hosts investigation.
Here’s something to consider, decrypted files and passwords
are stored in the RAM, and if they are available, investigating files that
might be encrypted in the hard disk can be a lot easier and the overall time of
the investigation can be considerably reduced.
We will be following up this particular article with an
in-depth review of the tools we have mentioned, with test cases.
Have fun and stay ethical.
About The Author
Abhimanyu Dev is a Certified Ethical Hacker, penetration
tester, information security analyst and researcher. Connect with him here



















0 comments:
Post a Comment