As you know that we have already shown you
how to configure web
server. Now it’s
time to move on to the next step which is the configuration of Web Application
in Ubuntu 18. So today we will be learning how can we configure the 5 famous
web applications (DVWA, bwapp, XVWA, SQLI, Mutillidae) in our web server for
Web Penetration Testing. So, let’s do that.
Table of
content
·
Requirement
·
Web
application
·
DVWA
·
bWAPP
·
Xvwa
·
Sqli
·
Mutillidae
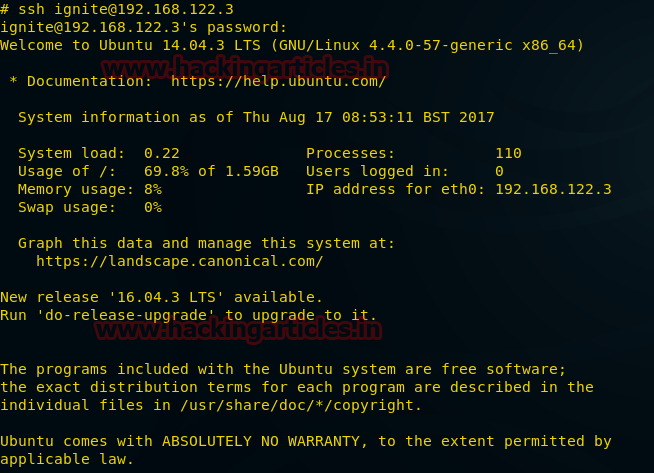
Requirement-ubuntu
18.0
Web Application
A web
application is a remote server software application. In general, web browsers
are used through a network, such as internet, to access Web applications. Like
a software program running on a desktop or desktop application, the Web-app
permits interaction with the user and can be designed for a wide range of
applications.
DVWA
Let’s start You should download and configure this web application only within the html directory for all web applications in the browser through localhost.
Go to your ubuntu terminal and move inside html directory by running the
following command and then download dvwa lab from the given link.
cd /var/www/html
git clone https://github.com/ethicalhack3r/DVWA
After the installation we will go inside the dvwa and there
we will find a config folder, now we will move inside the config folder and
there we will run the ls command to view all available folder, now here you
will see a config.inc.php.dist file. Now as you can see, we have moved config.inc.php.dist file to config.inc.php
cd /dvwa/config
mv config.inc.php.dist config.inc.php
Now open the config file by the following command; where you
will find that db user is root and db password is password.
Here you need
to make the changes and give access to the ubuntu user as in our case we have written
raj as db user and as our ubuntu password
is 123 so we have written 123 as db
password.
Now we will
try to open dvwa lab in the browser by the following URL and click on Create/Reset Database
http://localhost/dvwa/setup.php
Good! We have
successfully configured the dvwa lab in ubuntu 18 as we can see that we are
welcomed by the login page.
For login we
will use the dvwa username which is admin
and password which is dvwa password
by default.
bWAPP
A buggy web
application that is purposely unsafe. Enthusiasts of security, system engineers,
developers can find out about Web vulnerabilities and prevent them.
bWAPP
prepares you for successful tests and penetration testing. Now we will
configure bWAPP lab in Ubuntu 18. First, we will download bWAPP and then we
will move inside the Downloads folder and then unzip bWAPP file by the
following command-
unzip
bWAPP_latest.zip
Now we will move
bWAPP into var/www/html by the following command-
mv bWAPP /var/www/html
Now we will
edit the config file; so, move inside the config file by the following command
and where you can see that db username is root and db password is bug b
default.
cd admin
ls
nano setting.php
Now we will
make some changes and will set our ubuntu user raj in place of root and set password 123 in place of bug. Save it and then exit the config file.
Now go to
your browser and open bWAPP installation file by the following command and
click on here as shown in the image below
http://localhost/bWAPP/install.php
Now you will
get a login page of bWAPP where we will use the default username which is bee and default password which is bug and you are logged in in bWAPP.
Now you can
start working on bWAPP.
When you will
login as bee:bug; you will get the portal to test your penetration testing
skill.
XVWA
XVWA is
poorly coded written in PHP/MYSQL web application that helps security lovers
learn security from applications. This application is not advisable online
because it is Vulnerable to extremes as the name also suggests. This
application should be hosted in a controlled and safe environment where you can
improve your skills with the tool of your choice. So, let’s start-
First, we
will download XVWA from GitHub; so, go to ubuntu terminal and open the
following link to download XVWA lab inside html directory by the following
link-
git clone
https://github.com/s4n7h0/xvwa.git
Once it is downloaded,
we will open the config file of xvwa by the following command
cd
xvwa
nano
config.php
Now we ca see
that the username of xvwa is root and password is left blank.
Now we will
remove the root user from here and we will be using the ubuntu username and
password here which is raj:123
Afterwards we
will save the file and exit.
Now browse
web application through URL-localhost/xvwa and we can see that we are
successfully logged in-
SQLI Labs
A laboratory that offers a complete test environment for those interested in acquiring or improving SQL injection skills. Let’s
start. First, we will download SQLI lab inside html directory by the following
link-
Once the download is done, we will move sqli
labs into var/www/html directory and rename it to sqli. Then go inside the sqli
directory where we will find /sqli-connections
directory. Here we will run ls command to check the files and we can see that
here is file by the name of db-creds.inc
we need to
make some changes in the config file by the following command-
cd
Sqli_Edited_Version/
ls
mv
sqlilabs/ ../sqli
cd
sqli
cd
sql-connections/
ls
nano
db-creds.inc
As we can see
that username is given root and password is left blank which we need to modify.
Now here we
will set the username and password as raj:123
Now save the file and exit.
Now browse this
web application from through this URL: localhost/sqli and click on Setup/reset Databases for labs.
Now the sqli
lab is ready to use.
Now a page
will open up in your browser which is an indication that we can access
different kinds of Sqli challenges
Click on lesson
1 and start the Sqli challenge.
Mutillidae
OWASP
Mutillidae is a free open source purposely vulnerable web application providing
an enthusiastic goal for web security. It’s a laboratory which provides a
complete test environment for those who are interested in SQL injection
acquisition or improvement.
This is an easy-to-use Web hacking environment designed for laboratories, security lovers, classrooms, CTFs, and vulnerability assessment targets, and has dozens of vulnerabilities and tips to help the user.
So, let’s
start by downloading by the clicking on the following link given below-
git clone https://github.com/webpwnized/mutillidae
After the
download go inside the mutillidae directory and where you will find a directory
/includes, go inside this directory.
Inside this
directory we will find database-config.inc file which we need to open by nano
command as shown in the image below.
cd mutillidae
cd includes
ls
nano database-config.inc
Now here you
will find that username is root and password is mutillidae by default and which
we need to change.
Now we will
use our ubuntu username and password which is raj:123. Save the changes and
then exit
Now we will
open this our local browser by the following URL: localhost/mutillidae where we will find an option of reset
database. Just click on it to reset the database.
Now you will
be redirected to a page which will ask you to click ok to proceed. Here you
need to click on ok and you are done with the configuration of mutillidae lab.
So, In this
way we can setup our vulnerable web application lab for penetration testing.